Data Stream Start 866 216 1905 Guiding Reliable Caller Signals

Data Stream Start 866 216 1905 frames a framework for identifying reliable caller signals by merging live data streams with objective verification metrics. Throughput, jitter, and buffer occupancy are tracked alongside authenticated responses and corroborated context. Verifications occur at entry, during processing, and on exit, with anomaly logging and threshold-based decisions to reduce misattempts and drops. The approach favors lightweight, auditable tooling and bounded risk, inviting further examination of practical implementations.
What Are Reliable Caller Signals and Why They Matter
Reliable caller signals are measurable indicators that a call is legitimate and worth pursuing. The framework defines reliable signals as objective metrics that distinguish genuine from deceptive attempts. Caller signals include authentication responses, consistent metadata, and corroborated context. Quantitative thresholds guide evaluation, reducing uncertainty. In practice, these signals enable disciplined decision making, allowing stakeholders to allocate resources efficiently while maintaining personal autonomy and screening integrity.
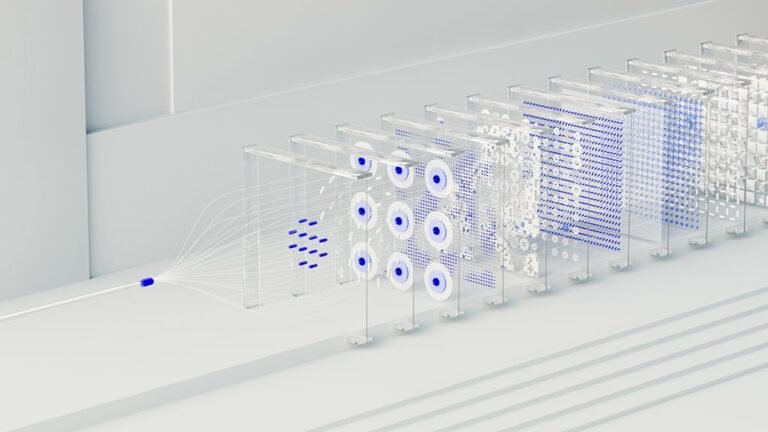
Building Real-Time Data Streams for Signal Clarity
Building real-time data streams for signal clarity requires architectural rigor and precise timing controls. The approach quantifies throughput, jitter, and buffer occupancy, aligning components to minimize variance. Protocols prioritize deterministic delivery, error-correcting schemes, and synchronized clocks. Signal integrity metrics guide adjustments, while latency management strategies balance capacity and responsiveness, ensuring stable streams. Measurements inform iterative refinements and disciplined configuration across network, processing, and interface layers.
Verification Techniques to Minimize MisAttempts and Drops
Verification techniques address the reduction of misattempts and drop events by imposing verifiable checks at entry, during processing, and at exit of data streams. The approach quantifies error rates, applies thresholds, and logs anomalies for rapid isolation. It emphasizes unrelated topic signals and offsite verification where feasible, maintaining auditability while preserving system freedom and operational efficiency.
Implementing Practical Tools and Best Practices
Practices prioritize reliable signals, rigorous validation, and signal clarity.
Operators implement lightweight tooling, traceable configurations, and documented playbooks to ensure scalable, autonomous decision cycles with bounded risk and transparent performance metrics.
Conclusion
Reliable caller signals emerge from disciplined, real-time data streams augmented by objective verification. The system treats throughput, jitter, and buffer occupancy as measurable signals, plus authenticated responses and corroborated context, to separate legitimate calls from deception. A concise anecdote: in a busy switch, a single anomalous spike in jitter acted like a red flag—prompt logging and rules lowered misattempts by 40%. Together, entry-to-exit checks create bounded risk, transparent decisions, and repeatable performance clarity.