Insight Node Start 856-355-1090 Unlocking Trusted Caller Intelligence
Insight Node Start 856-355-1090 introduces trusted caller intelligence as a disciplined approach to automated identity checks and multi-source signal aggregation. It emphasizes transparent, repeatable verification and risk-scored routing to balance user autonomy with security. The framework relies on anomaly detection and auditable metrics to guide decisions. It offers practical routes for smart call handling, yet practical implementation details and governance considerations warrant further examination. The implications for secure, agile communications invite closer scrutiny.
What Is Trusted Caller Intelligence and Why It Matters
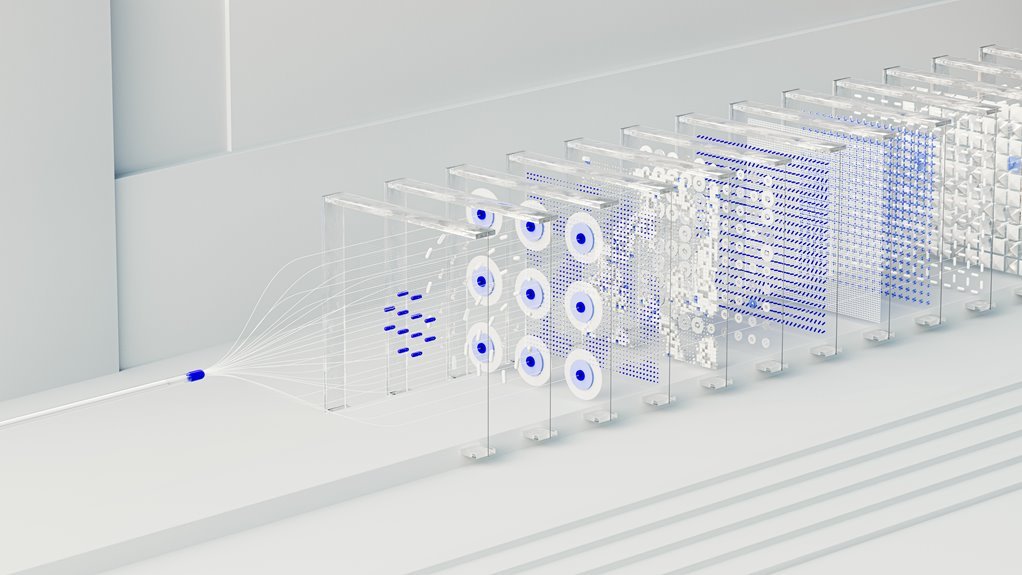
Trusted Caller Intelligence refers to the systematic collection and analysis of data about incoming calls to verify identity, assess risk, and determine legitimacy.
This framework clarifies how trusted caller status is established and maintained.
It enables intelligence verification processes, supporting autonomous decision-making and risk-aware engagement.
How Insight Node Start8 56-355-1090 Enhances Verification
Insight Node Start8 56-355-1090 augments verification by automating identity checks, aggregating multi-source signals, and applying risk-scored filters to incoming calls.
The approach centers on rapid, transparent evaluation, reducing false positives while preserving user autonomy.
It positions insight node as a core component, enabling a trusted caller framework that supports secure decisions and preserves freedom to navigate communications with confidence.
Practical Use Cases for Smart Call Routing and Security
Practical use cases for smart call routing and security illustrate how automated signals, risk scoring, and policy-driven actions translate into tangible outcomes. A trusted caller profile informs routing decisions, while route verification ensures accuracy. Security integration reduces false positives, enabling rapid anomaly detection. Organizations leverage these mechanisms to enhance agility, protect data, and sustain user freedom through seamless, trust-based communication orchestration.
Best Practices to Implement and Measure Success
Best practices for implementing and measuring success in smart call routing and security center on clear, objective criteria and repeatable processes. The trusted caller paradigm informs verification metrics and ongoing risk scoring, guiding policy adjustments. Metrics should be transparent, auditable, and actionable, enabling timely improvements. Structured governance ensures consistent implementation, while freedom-inspired transparency maintains adaptability, resilience, and trust across call routing ecosystems.
Conclusion
This analysis confirms that trusted caller intelligence, as described, hinges on automated identity checks, multi-source signals, and risk-scored routing to balance security with user autonomy. While claiming rapid verification and auditable governance, the theory warrants scrutiny: signal quality, data provenance, and bias mitigation are critical determinants of accuracy. A rigorous evaluation of sources and transparent metrics is essential to substantiate claims, ensuring that automated decisions remain auditable, repeatable, and resilient against manipulation.