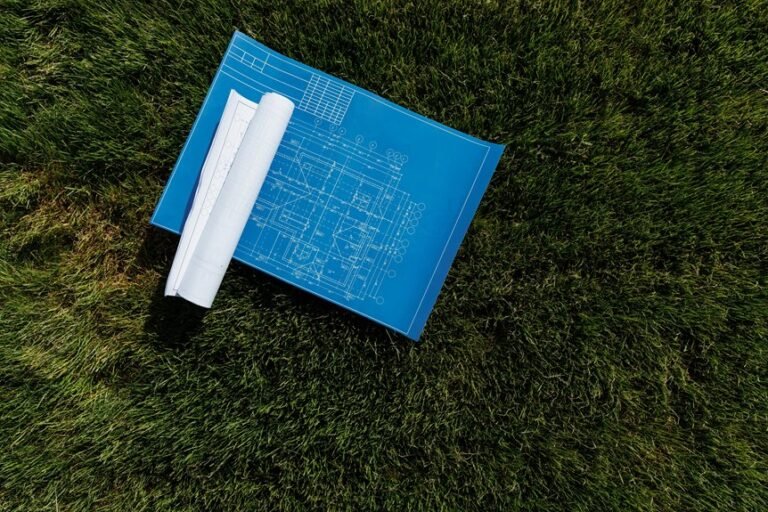
Digital Machine 4t1bf1fkofu95773 Blueprint

The Digital Machine 4t1bf1fkofu95773 Blueprint presents a modular, interoperable framework with clear core outcomes. It emphasizes disciplined deployment, auditability, and predictable performance through standardized interfaces and defined component responsibilities. Governance translates into auditable workflows and continuous monitoring, while risk management remains transparent and evolving. Scaling and troubleshooting are data-driven and repeatable, supported by resilient delivery and preserved user autonomy. The approach invites scrutiny of its practical interfaces and governance workflows, suggesting a careful path forward.
What the Digital Machine Blueprint Delivers
The Digital Machine Blueprint delineates the core outcomes and capabilities the system delivers, framing its value in concrete terms rather than conjecture. It establishes measurable results, including privacy guidelines and data minimization, while outlining robust security controls and access governance. The framework enables disciplined deployment, auditability, and predictable performance, offering freedom through transparent standards, repeatable processes, and principled decision-making.
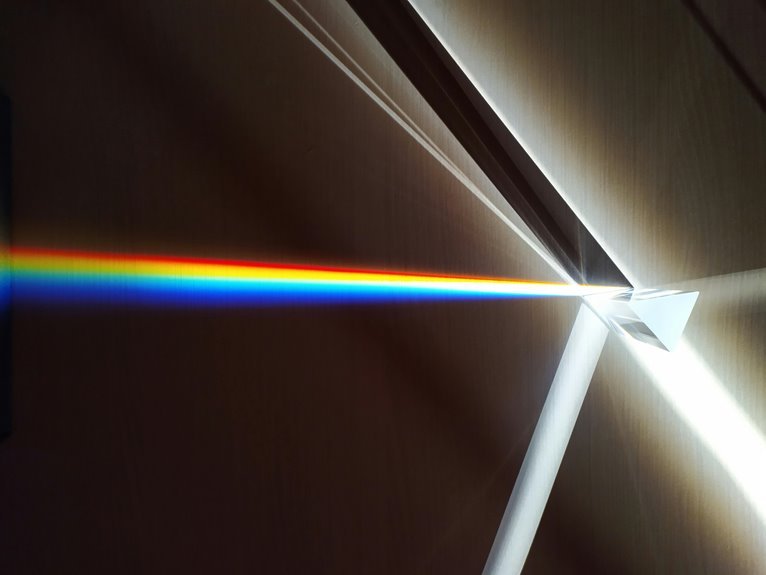
How the Modular Components Fit Together
How do the modular components interlock to form a cohesive whole? The architecture emphasizes standardized interfaces and clearly defined responsibilities, enabling predictable assembly. Modular interfaces provide controlled points of interaction, while component interoperability ensures data and control flows remain consistent across boundaries. This disciplined coupling supports adaptability, minimizes coupling, and preserves system integrity, allowing independent evolution without disrupting overall functionality or user autonomy.
Privacy, Security, and Compliance in Practice
Privacy, security, and compliance practices are examined through a structured lens that links policy, architecture, and operations to measurable risk outcomes.
The analysis filters governance into concrete workflows, highlighting privacy risks and security controls as essential mechanisms.
Practitioners map controls to real-world processes, assess residual risk, and enforce continuous monitoring, ensuring compliance stance remains transparent, flexible, and auditable across evolving threat landscapes.
Scaling, Troubleshooting, and Roadmapping the Future
This approach emphasizes scalable architectures, disciplined experimentation, and data-driven prioritization.
It outlines scaling strategies, clarifies failure modes, and codifies troubleshooting best practices, enabling resilient delivery while preserving organizational freedom and continuous improvement through transparent, repeatable processes.
Conclusion
The Digital Machine blueprint, analyzed dispassionately, reveals a coherent theory: modular, interoperable components yield predictable outcomes while preserving autonomy and governance. By standardizing interfaces, it enables auditable risk management and repeatable scaling, aligning with disciplined deployment and transparent performance metrics. The theory holds that privacy, security, and compliance are not afterthoughts but core, intrinsic guards embedded in architecture, not bolted on. In practice, observability and governance drive continual improvement, guiding future roadmaps without compromising system integrity or user trust.